CodeMantle: Distributed OpenCode Control Plane
CodeMantle is the system I built to solve one concrete problem: my best machine stayed at home, but my coding day did not.
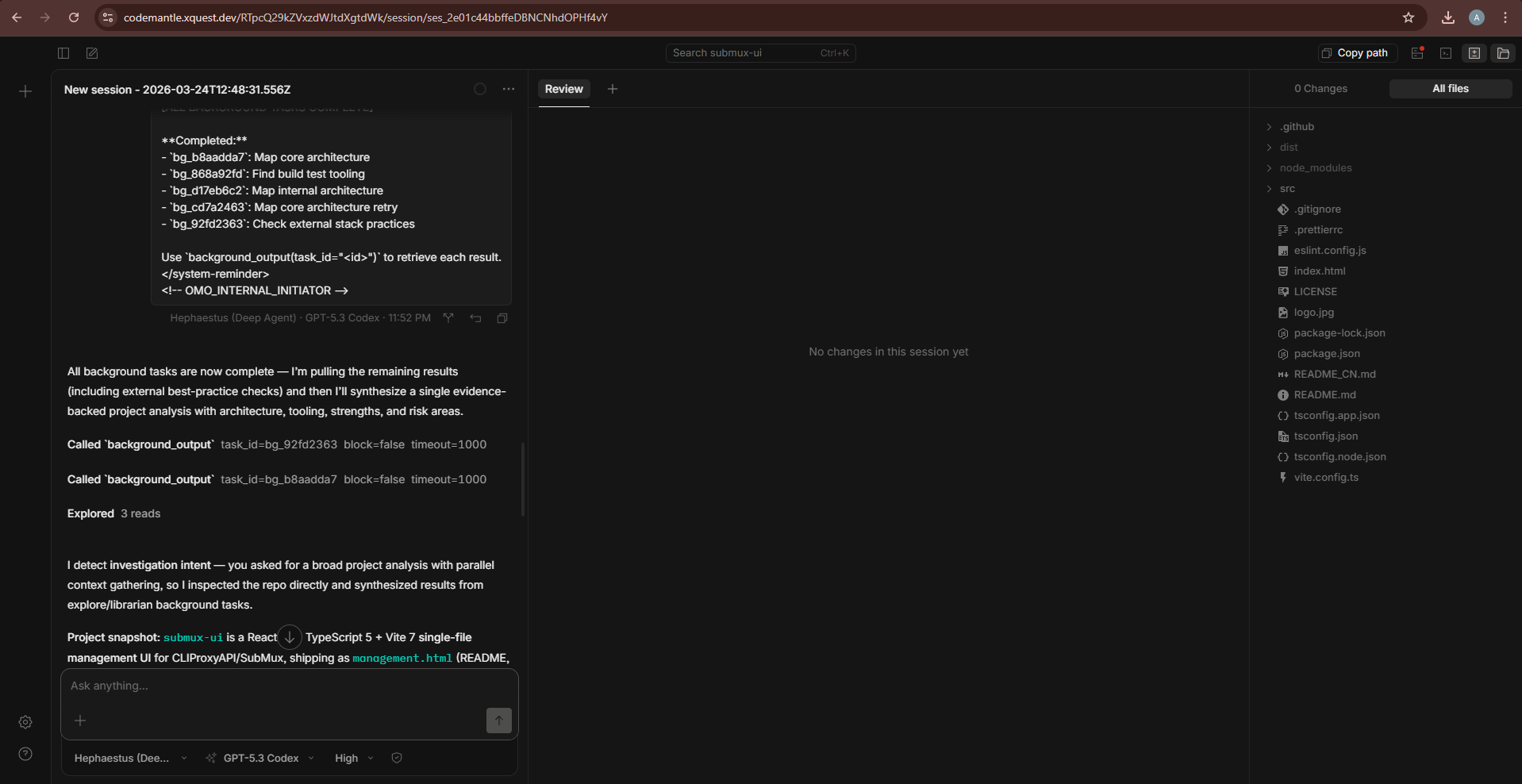
I wanted to start and operate OpenCode sessions remotely, from any location, without exposing unrestricted shell access to the host.
Why this project matters
Most remote coding setups optimize for convenience first and boundaries later. CodeMantle flips that:
- Convenience: start and monitor OpenCode remotely.
- Containment: daemon-enforced filesystem and process boundaries.
- Control: role-gated operations and just-in-time credential handling.
This produces a workflow that feels location-independent while still respecting host-local trust boundaries.
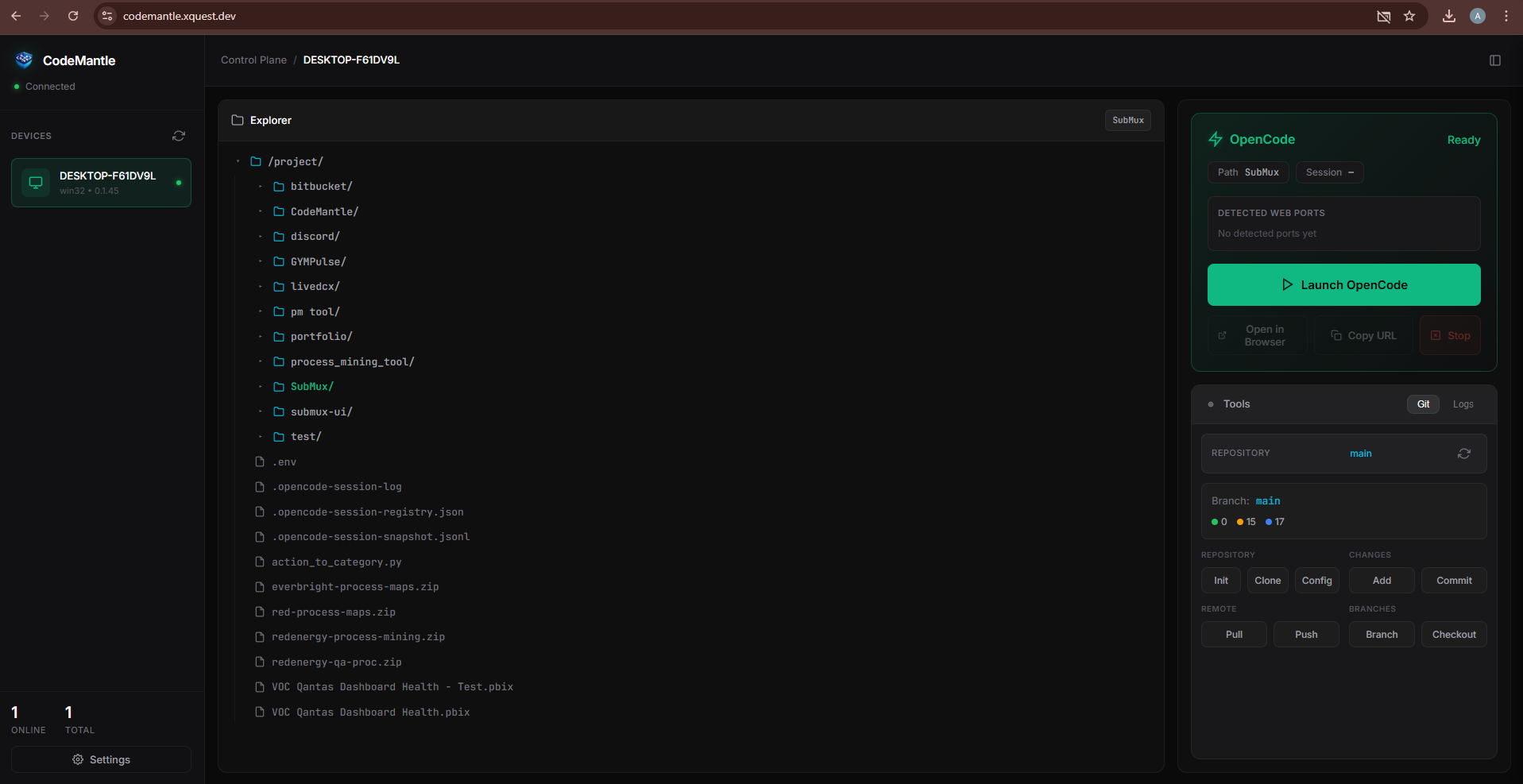
What the operator experience looks like
The product experience is intentionally visual and operational, not abstract.
At the top level, operators can immediately identify which host is online, which workspace is active, and where intervention is required.
When an operator starts a session remotely, every action is routed through policy checks and ownership scope before execution.
Technical architecture (split-plane by design)
The architecture is split because trust responsibilities are split:
- Control plane ('@codemantle/panel'): identity, RBAC, route authorization, orchestration API/UI.
- Agent daemon ('@codemantle/agent-daemon'): host-local boundary enforcement and OpenCode lifecycle control.
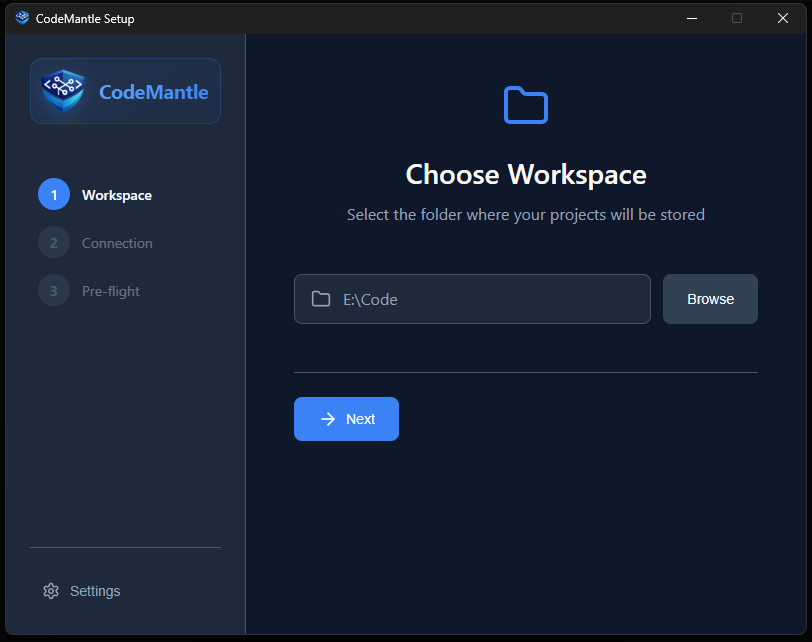
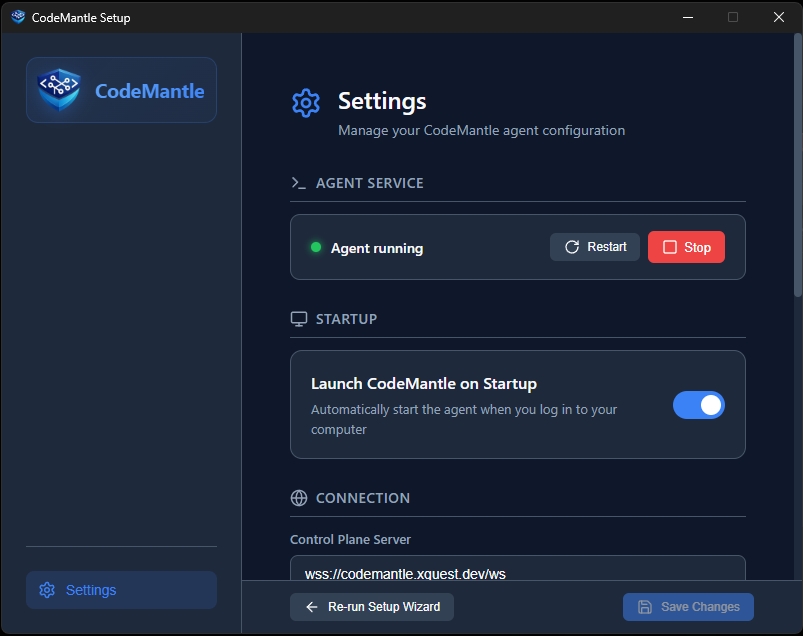
- Desktop operator app (Tauri): setup, sidecar lifecycle, tray/autostart controls.
- Unified CLI ('codemantle'): entry point for panel/agent bootstrap flows.
Request path and trust boundaries
Runtime transport uses reverse WebSocket connectivity from daemon to control plane. No inbound port needs to be opened on the managed host.
Security controls are applied at both planes:
- Role-gated API access ('viewer', 'operator', 'admin', 'owner')
- CSRF checks on mutating routes
- Nonce + timestamp + HMAC handshake ('h1'/'h2')
- JIT credential binding with TTL and kill switch semantics
- Root/path/symlink containment checks before local operations
Deployment posture
- Public TLS edge on 443 (Nginx/Caddy/Traefik)
- Internal WS/API listeners behind reverse proxy
- PM2/systemd process supervision
- Outbound 'wss' daemon connectivity from managed hosts
Reliability and current caveat
CodeMantle includes heartbeat/reconnect logic, bounded retries, and continuity artifacts for restart recovery.
Current caveat: some live routing/session ownership state is still in-memory, so multi-instance horizontal scaling requires shared-state coordination.
Links
- Repository: https://github.com/XQuestCode/CodeMantle
- Unified CLI: https://www.npmjs.com/package/codemantle
- Panel package: https://www.npmjs.com/package/@codemantle/panel
- Agent package: https://www.npmjs.com/package/@codemantle/agent-daemon
- Architecture docs: https://github.com/XQuestCode/CodeMantle/blob/main/docs/architecture.md
- Security model: https://github.com/XQuestCode/CodeMantle/blob/main/docs/security-model.md
- Deployment guide: https://github.com/XQuestCode/CodeMantle/blob/main/docs/deployment.md